CryptoDeepTools FINAL Hacking collection! 31 modules
Seller:
Feedback:
2
0
0
Rating: 100.0% (2)
Member Since:
Feb 27th, 2024
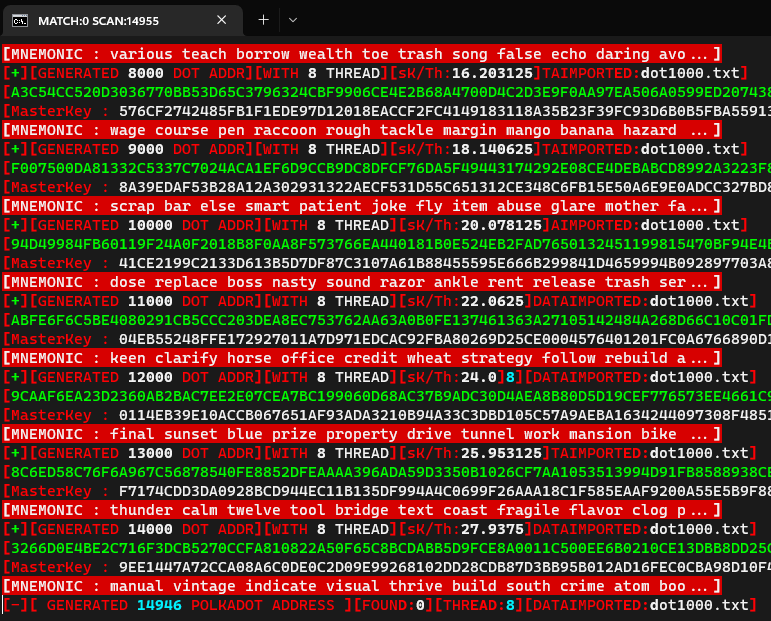
- CryptoDeepTool is a FULL collection with 31 modules with full and detailed toturials with how to do each attack in google colab.
ALL needed tools and softwares included to do ALL attack. So if you have wanted to learn to hack bitcoin here is the easiest and
most included collection with everything from wallet recovery on seeds, passwords wallet.dat to search engine crawler that collecting
qr codes with private keys from google , bing and so on. Very easy toturials in english and russian.
- Crypto Deep Tools a set of scripts for detailed cryptanalysis of the Blockchain network in cryptocurrency Bitcoin
#01. BlockchainGoogleDrive
- Parsing Blockchain in Google Drive
#02. BreakECDSAcryptography
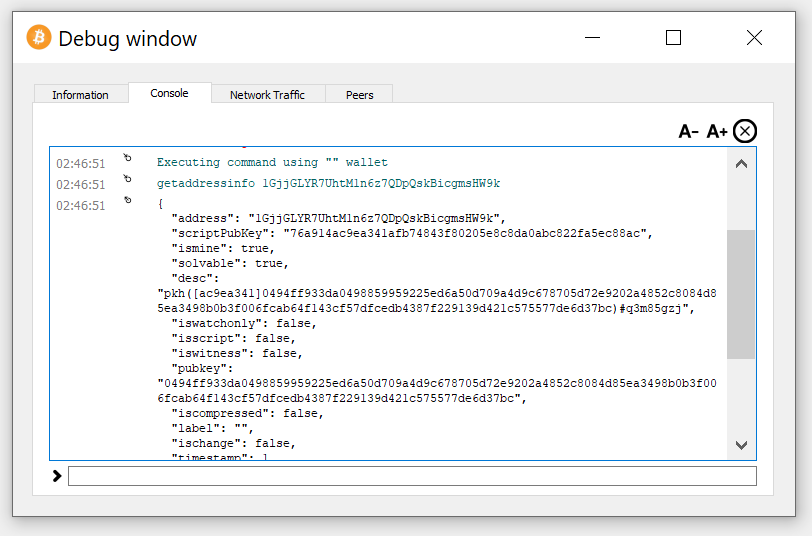
- Analyze the data from the file "RawTX.json". Script breakECDSA.py reconstructs the unsigned message for each to find the Z value.
The result is returned as R, S, Z, PUBKEY for each of the inputs present in the data in the "RawTX.json" file.
#03. CheckBitcoinAddressBalance
- Check Bitcoin Address Balance: Script pubtoaddr.py Converts PUBKEY (HEX) to Bitcoin Address (Base58) // Script bitcoin-checker.py
Checks the balance by scanning the Blockchain
#04. AlgorithmsForSecp256k
- Useful and Efficient Elliptic Curve Algorithms secp256k1
- Algorithm for generating a point on the curve E
- Algorithm for adding points
- Point doubling algorithm
- Algorithm for finding the integer multiple point
- Algorithm for finding an integer multiple point (Scalar multiplication)
- Algorithm for generating a divisor D over a curve E with a carrier supp(D) of a given size d
- Miller's algorithm for calculating the value of the Weil function f n, P from a divisor D such that supp(D) ∩ {P, O} = ∅
- Weil pairing
#05. VulnerableOpenSSL
- Vulnerable to Debian OpenSSL bug (CVE-2008-0166)
#06. KangarooJeanLucPons
- Pollard's kangaroo method computes discrete logarithms in arbitrary cyclic groups. It is applied when the discrete logarithm is
known to lie within a certain range, say [ a , b ], and then has the expected time to execute the bulk operation. One way to break
ECDSA signature schemes is to solve the discrete logarithm problem.
#07. EndomorphismSecp256k1
- Secp256k1 acceleration function using endomorphism which helps in optimizing ECDSA validation for bitcoin cryptocurrency.
#08. ReducePrivateKey
- In this repository, we will use scripts that will help reduce the private key knowing only the leak from the "BLOCKCHAIN FOLBIT LEAKS"
list and the public key from "UTXO".
#09. BitcoinWalletRecovery
- We all know that the disclosure of the private key in the ECDSA signature can lead to the complete recovery of the Bitcoin Wallet.
In our earlier articles, we looked at weaknesses and vulnerabilities in blockchain transactions, but there are also ECDSA short
signatures that also lead to the full recovery of a Bitcoin Wallet.
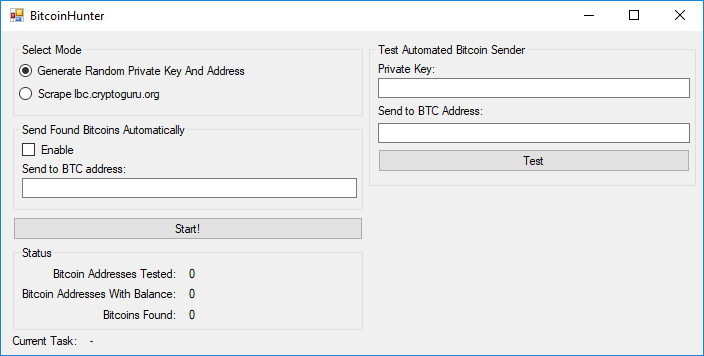
#10. MrRobotQR
- MrRobotQR is an open source script that automates the process from entering a search keyword to deriving the private key of a Bitcoin wallet.
#11. QianshiBTC
- QBitcoin Address Collision Finder
#12. CoingeckoAgentFtpupload
- Coingecko-VanityGen is a command-line utility that can generate cryptocurrency addresses given initial parameters. Coingecko-VanityGen
works with GPU runtime support (Google Colab) and generates beautiful crypto wallet addresses for the full list of the Coingecko aggregator
according to its own parameters. The selection of the utility is based on a probabilistic search, which takes some time. The time depends
on the complexity of the given template, computer speed and luck. To increase the speed of generating cryptocurrency addresses, there is
oclvanitygen - which uses OpenCL-compatible GPUs.
#13. TeslaBrainWallet
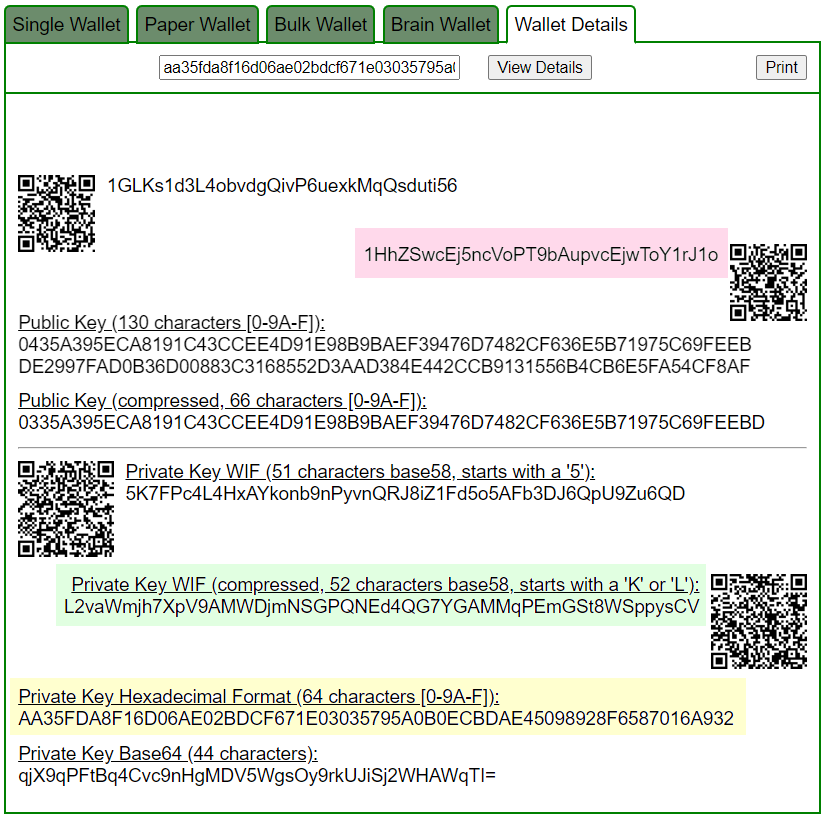
- There are many forms to create a Bitcoin wallet. One of the first methods to create a Bitcoin wallet was known as BrainWallet.
BrainWallet is convenient in the sense that it allows you to store a "passphrase" in memory or in a notebook. The passphrase is
hashed using the SHA-256 algorithm, and is used as the seed to generate the private key. Due to its popularity and ease of use,
many BrainWallets over the past few years have been used with weak passphrases. This weak private key generation method allowed
attackers to steal quite a lot of BTC coins by simply cracking the password against the hashes stored on the blockchain. Let's
move on to the experimental part:
#14. FreyRuckAttack
- With a critical vulnerability in the Bitcoin blockchain transaction, we can solve the rather difficult discrete logarithm problem to
extract the secret key "K" (NONCE) from the vulnerable ECDSA signature in order to ultimately restore the Bitcoin Wallet, since knowing
the secret key we can get a private key. To do this, there are several algorithms from the list of popular attacks on Bitcoin, one of
which is the “Frey-Rück Attack on Bitcoin”.
#15. RowhammerAttack
- The biggest cryptographic strength of the Bitcoin cryptocurrency is a computational method in discrete mathematics that takes the
factorization problem of large integers and the hidden number problem (HNP) in the Bitcoin ECDSA signature transaction as a basis.
Rowhammer Attack on Bitcoin, allows us to efficiently find all zeros for normalized polynomials modulo a certain value, and we adapt
this method to the ECDSA signature algorithm, more precisely to critically vulnerable transactions in the Bitcoin blockchain. We will
apply ECDSA signature differential failure analysis and obtain a private key from a transaction for different Bitcoin Wallets.
#16. WhiteBoxAttack
- We will again touch on the topic of a signature failure in a blockchain transaction and apply a completely new attack: “WhiteBox Attack
on Bitcoin” . Differential fault analysis (DFA)was briefly described in the literature in 1996 when an Israeli cryptographer and cryptanalyst
Eli Biham and an Israeli scientist Adi Shamir showed that they could use error injection to extract the secret key and recover the private key
using various signature and verification algorithms.
#17. BTCRecoverCryptoGuide
- In this article, we will take a detailed look at the open source password recovery tools and wallet seed phrases in the Crypto Deep Tools repository, and we will also discuss the situation when you accidentally lost or forgot part of your mnemonic or made a mistake while decrypting it. (So you either see an empty wallet or get an error that your seed is invalid) For wallet password or passphrase recovery, it is primarily useful if you have a reasonable idea about what your password might be.
#18. TwistAttack
- In this article, we will implement a Twist Attack with an example and show how, using certain points on the secp256k1 elliptic curve, we can get partial private key values and restore a Bitcoin Wallet within 5-15 minutes using “Sagemath pollard rho function: (discrete_log_rho)” and “ Chinese Remainder Theorem” .
#19. SageMathGoogleColab
- Google Colab has been updated to "Ubuntu 20.04.5 LTS". To perform cryptanalysis, we will install a new version of SageMath version 9.3.
#20. PolynonceAttack
- POLYNONCE ATTACK we use BITCOIN signatures as a Polynomial to an arbitrarily high power of 128 bits to get a Private Key
#21. LatticeAttack
- LATTICE ATTACK 249bits we solve the problem of hidden numbers using 79 signatures ECDSA
#22. SmartContractVulnerabilities
- Solidity Forcibly Send Ether Vulnerability to a Smart Contract continuation of the list of general EcoSystem security from attacks
#23. SolidityVulnerableHoneypots
- Phenomenon from Blockchain Cryptocurrency Solidity Vulnerable Honeypots
#24. ShellShockAttack
- ShellShock Attack vulnerability on “Bitcoin” & “Ethereum” server discovered in GNU Bash cryptocurrency exchange
#25. MilkSadVulnerability
- On August 10, 2023, a group of Bitcoin security researchers identified a vulnerability in the Libbitcoin Explorer 3.x library. This
critical vulnerability allowed attackers to steal more than $900,000 from Bitcoin Wallet users, according to a report from blockchain
security firm SlowMist. The vulnerability may also affect Ethereum, Ripple, Dogecoin, Solana, Litecoin, Bitcoin Cash and Zcash users
who use Libbitcoin to create accounts. The vulnerability, dubbed "Milk Sad", was first discovered by cybersecurity team Distrust. This
Bitcoin-threatening vulnerability allows attackers to gain access to the private keys of a crypto wallet using the Mersenne Twister
pseudo-random number generator (PRNG), which leads to disastrous consequences. In our last article, we clearly showed an example of
such an attack on Bitcoin Wallets. Let's look at two examples with a total loss: 40886.76 USD // BITCOIN: 1.17536256 BTC and a second
example with a total loss: 19886.91 USD // BITCOIN: 0.58051256 BTC
#26. BitcoinLightningWalletVulnerability
- In this repository, we will focus on the popular Bitcoin Wallet application for iOS and Android smartphones with support for fast
payments through the Lightning network BLW: Bitcoin Lightning Wallet. Unfortunately, many autonomous nodes of the open source mobile
application from LNbits Node Manager and Core Lightning are exposed to a HIGH RISK of losing all funds in various cryptocurrency coins.
Developer David Shares from the Japanese company Bitcoin Portal published a chronological list that shows that the Lightning Network is
drowning in technical problems, bugs, shortcomings, criticisms and exploits. It is an over-promised technology that does not provide
decentralization and is still far from being functional and secure for users. Look at example with a total loss: 11032.77 USD // BITCOIN:
0.30412330 BTC
#27. PaddingOracleAttackonWalletdat
- Padding Oracle Attack This method is a side-channel attack on the Bitcoin Core cryptosystem that uses leaked data from a poorly
implemented decryption routine to completely undermine the cryptosystem. An attacker can effectively decrypt the data in the
wallet.dat file without knowing the decryption key if the target system leaks whether a padding error occurred when decrypting
the ciphertext. Let's look at an example with a total loss: 44502.42 US dollars // BITCOIN: 1.17461256 BTC
#28. DustAttack
- "Dust Attack" known as: "Dusting Attack" or "Crypto Dust". Perhaps every cryptocurrency user or holder of a large amount of BTC, ETH coins
replaced the receipt of an insignificantly small amount of coins in satoshi on their cryptocurrency wallet, this receipt is disguised as
“Donate”, but in fact it is a whole mathematically refined system for taking away all the accumulated coins of the wallet for balance.
Let's look at two different examples of dust attacks to shed light on all the intricacies of this manipulation and what risks can await
users and holders of the popular cryptocurrency Bitcoin. To carry out a dust attack, confirmation of isomorphism by miners plays an
important role, because From 2022 to 2024, many cryptocurrency services and hardware wallets are actively fighting the dust attack. At
the moment, the method of independently creating dust transactions on your own cold wallet has become widely popular. Let's transform the
dust transaction into isomorphism, according to the theory, two transactions must be confirmed by miners. Having created the RawTX of
the dust attack, we send a small amount of 555 satoshi, then we receive an isomorphism of the first transaction, where a reverse transfer
of funds occurs from the balance of the victim of the dust attack.
#29. BitcoinUtilities
- Bitcoin utilities are numerous and varied. Its decentralized nature and lack of intermediaries make it a powerful tool for a variety of
use cases. As the technology continues to evolve and mature, we can expect to see even more innovative applications of Bitcoin in the future.
#30. GaussJacobiMethod
- Application of the Gauss-Jacobi method for a cryptographic task - decrypting the password of the wallet.dat file for a Bitcoin wallet.
The modification of the algorithm emphasizes its mathematical basis, explaining the process, how this method can be adapted to work with
cryptographic tasks, in particular, with decrypting the password of a cryptocurrency wallet.
#31. BlockchainAPI
- The scientific article explores the possibilities of integrating blockchain technologies with web services and APIs. Discusses the
benefits of using blockchain APIs to improve the security, transparency and efficiency of web applications. Examples of successful
blockchain projects are given and prospects for the development of this area are discussed.